In this article, we will cover onboarding Windows Server to Microsoft Defender for Endpoint by using local script.
Before deploying it let’s understand what is Microsoft Defender for Endpoint and how it works?
Microsoft Defender for Endpoint is a unified endpoint security platform provided by Microsoft to help protect enterprise systems and data from advanced threats. It offers advanced threat protection, detection, investigation, and response capabilities for endpoints such as computers, laptops, servers, and mobile devices.
Key features of Microsoft Defender for Endpoint include:
- Endpoint Protection: It provides real-time protection against viruses, malware, and other malicious software.
- Endpoint Detection and Response (EDR): It offers advanced threat detection and response capabilities, allowing security teams to investigate and respond to suspicious activities, incidents, and breaches.
- Advanced Threat Analytics: It uses behavioral analytics and machine learning to detect unusual or suspicious behavior on endpoints, helping to identify potential threats that might go unnoticed by traditional antivirus solutions.
- Attack Surface Reduction: It helps minimize the attack surface by controlling and limiting the execution of potentially malicious scripts, files, and applications.
- Network Protection: It includes features to help protect endpoints from network-based attacks and exploits.
- Automated Investigation and Remediation: It offers automated investigation and remediation of common security incidents, saving time for security teams.
- Threat Intelligence: It leverages Microsoft’s extensive threat intelligence data to help identify and block known threats.
- Integration with Microsoft 365 Security Center: It provides a centralized dashboard for security operations and incident management, allowing security teams to monitor, manage, and respond to security events.
Overall, Microsoft Defender for Endpoint aims to provide comprehensive endpoint security by combining traditional antivirus capabilities with modern threat detection and response features, helping organizations to better protect their digital assets from a wide range of cyber threats.
To check different Defender for Endpoint plans and features, click here.
Download the Microsoft Defender for Endpoint Onboarding Package
In this step, we will cover how can we download the onboarding package from the Microsoft 365 Defender portal.
- Login with your Security or Global Administrator credentials to the Microsoft 365 Defender portal by clicking here.
- In the left navigation pane, scroll down and locate to Settings and click on Endpoints options from the list.
- Now, in the middle pane, scroll down and look for Onboarding option under Device management section.
- In the Select operating system to start onboarding process, choose Windows Server 2019 and 2022 option. As package is same for Windows server 2019 and 2022 as of now.
- In the Deployment method, choose Local Script option because we are going to deploy it through local script. We have another 3 methods which we can choose based on our deployment method.
- Finally, click on Download onboarding package to download the package.

Deploying the Onboarding Package
- Login to your Windows server using an Admin credentials.
- Copy the onboarding package to the machine which we downloaded earlier in the downloading steps above.
- Once copied, right click on the file and extract it to a location on your machine, open the extracted folder.
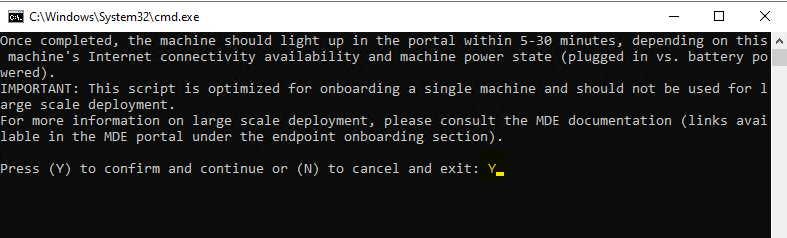
- Right click on the Onboarding package script and choose Run as administrator and type “Y” when it asked in the Command Prompt. We can run this through Command Prompt also by locating to the onboarding package path e.g., C:\Users\username\Downloads\WindowsDefenderMDE.
Once the onboarding process is done, it will show as Successfully onboarded machine to Microsoft Defender for Endpoint. Now you can check this device entry on the Microsoft 365 Defender portal. However, sometime it may sometime to reflect over the portal.
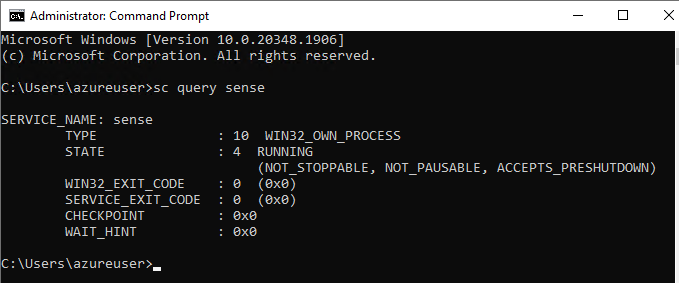
Check the status if Defender for Endpoint services are running
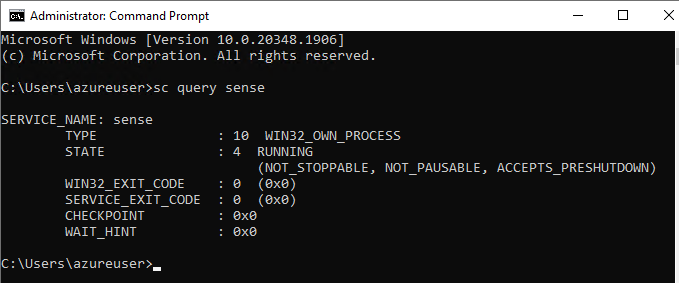
To check the status of Microsoft Defender for Endpoint services are running on the machine.
Open Command Prompt as an Administrator and type command: sc query sense
In the below screenshot, we can see the state as running.
To check the status of the device in Microsoft 365 Defender portal.
- In the left navigation pane, click on Devices under Assets.
- Here, you will be able to see your newly onboarded machine.
Wrapping up Onboarding Windows Server to Microsoft Defender for Endpoint
So, in this way we have successfully onboarded the Windows Server 2022 machine to the Microsoft Defender for Endpoint portal. We used local script deployment method to onboard the device. The ways for onboarding a device to the portal depends on the type of Operating System.
Troubleshoot Microsoft Defender for Endpoint issue
I have seen many issues related to Defender for Endpoint like device is not showing over the Defender portal, health issues, last device update status or exposure level not showing. So, to troubleshoot these types of issues, Microsoft have an tool called as Microsoft Defender for Endpoint client analyzer. This tool can be downloaded from the Microsoft’s official website by clicking here.
Here are the steps to run the Microsoft Defender for Endpoint client analyzer tool and collect the logs for further troubleshooting:
- Visit the Microsoft’s official website to download the tool by clicking here.
- Download the tool based on your Operating System (it can be Beta version too).
- Once the tool is downloaded, extract it and then open it.
- Copy the path of the tool.
- Launch Command Prompt as an Administrator.
- Change the path to the file location.
- Now press Tab key until it shows MDEClientAnalyzer.cmd in the command prompt and press Enter key.
- Click on Accept the License terms & conditions if prompts.
- It will take some time to collect the logs. (Note: it may take screenshots, can fetch IP etc. so be careful while sharing with others)
- Once it collect the logs, will ZIP it and stores in the same location from where you executed this script. We can find more details in the MDEClientAnalyzer.html file which is generated after running the tool.
- We can use this logs for further troubleshooting steps if required.
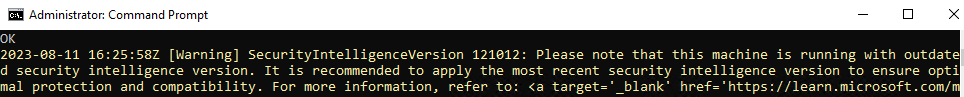
- I ran this tool and got the below Warning message:
Please note that this machine is running with outdated intelligence Version. It is recommended to apply the most recent security intelligence version to ensure optimal protection and compatibility.
Please note that this machine is running with an outdated version of Defender Antivirus engine. After a new package version in released, support for the previous two versions is reduced to technical support only.
Please note that this machine is running with an outdated versions of Defender Platform. Platform versions older than N-2 no longer be supported.
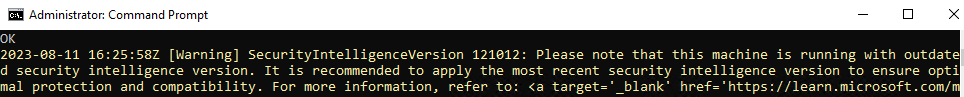
The above warnings means, in our machine these tools are running with outdated versions and our devices will stop sending data to the Microsoft 365 Defender portal.
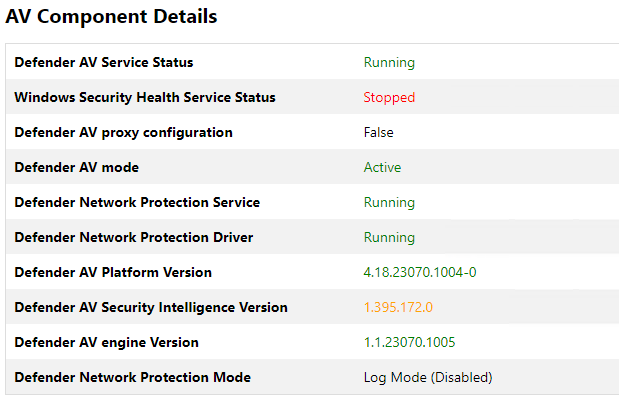
In the above screenshot, we can see Defender AV Security Intelligence Version is showing in Yellow color while are showing in Green which means it is outdated and we need to update it.
To fix these issues, download and install the latest versions of Security intelligence, Defender antivirus engine and Defender platform manually.
We recommend keep checking on the latest versions of these security updates. Click here to check the latest versions of these updates. If you find any of these are outdated, download and install it by clicking on the direct URL.
So, in this way we learn how to troubleshoot the issues related to Microsoft Defender for Endpoint.
If you wish to be connected with us for more technical perspective, please follow us.